Patents Related to CCP-Backed Silk Typhoon Hackers Reveal Capabilities
Patents Related to CCP-Backed Silk Typhoon Hackers Reveal Capabilities - A recently unsealed indictment named companies tied to the CCP hackers that hold patents for tools for data collection from Apple computers and data scanning.

.
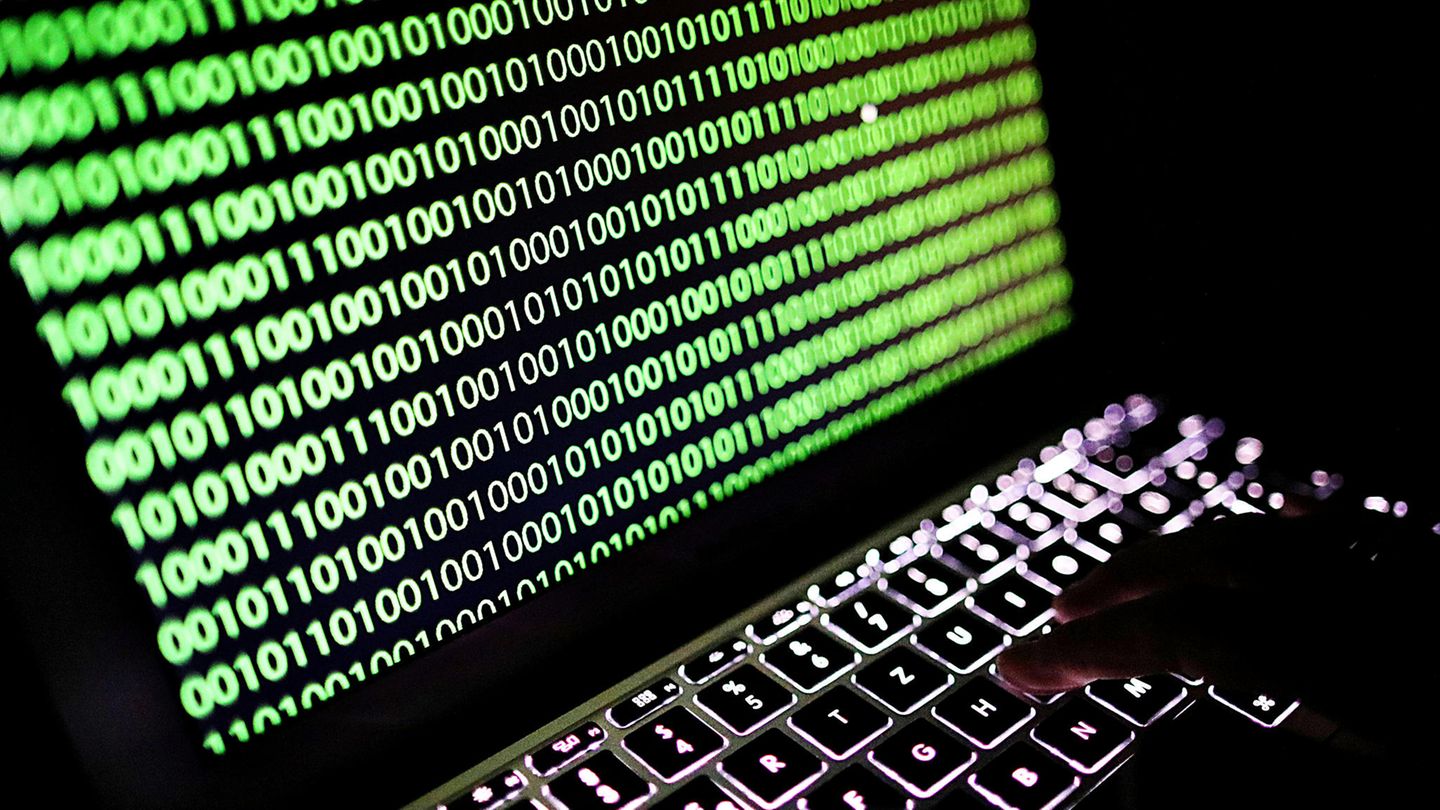
Cybersecurity research firm SentinelOne has identified more than 10 patents held by companies that are associated with the Chinese Communist Party (CCP)-backed hacking campaign known as Hafnium, or Silk Typhoon, revealing “highly intrusive forensics and data collection technologies.”
SentinelLabs notes that while the group was responsible for the initial Microsoft Exchange breach, Hafnium/Silk Typhoon’s activity was immediately followed by other threat groups that “flooded the zone” with their own exploitation attempts.
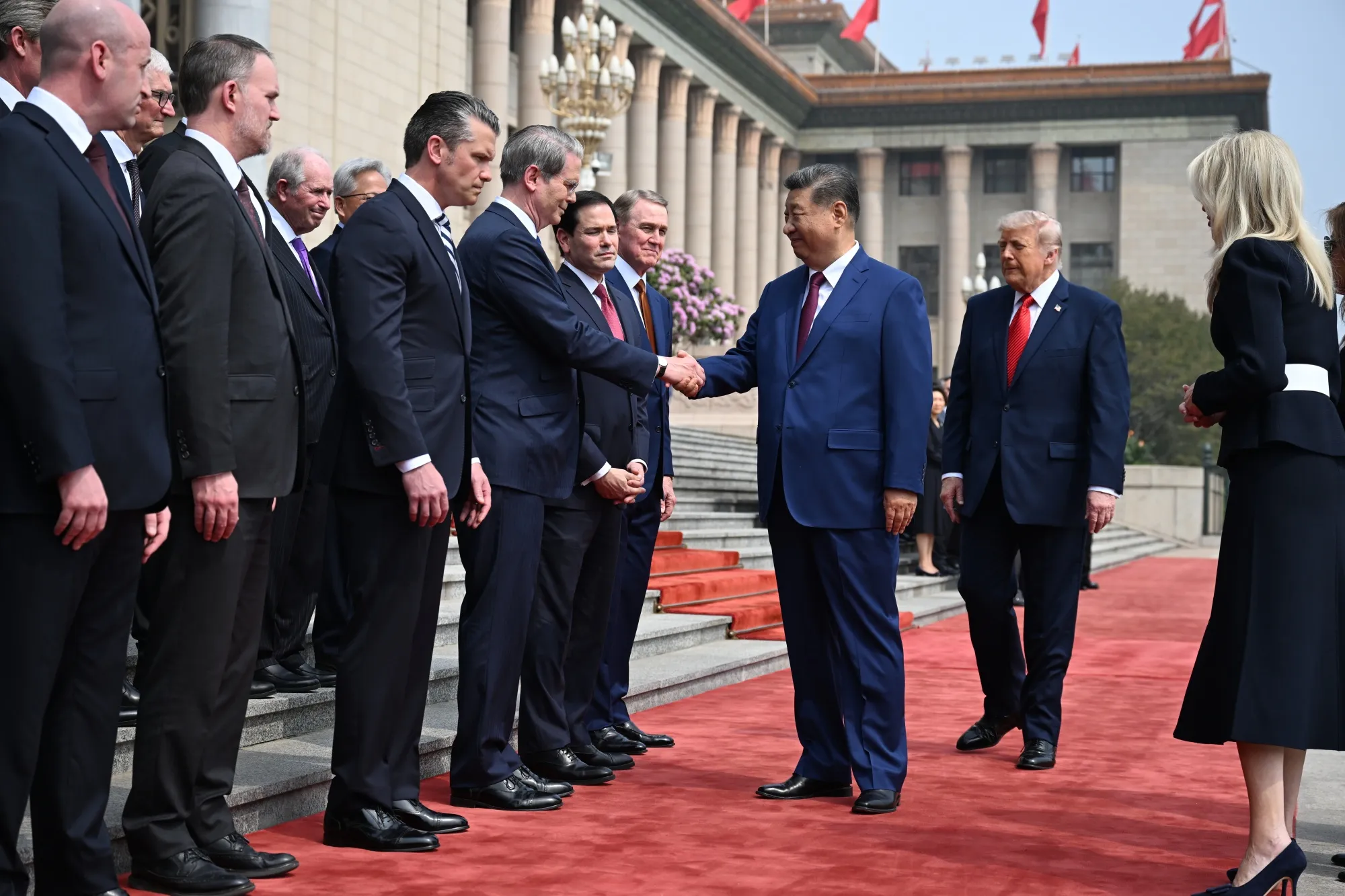
Xu was a general manager at Shanghai Powerock Network Co., and Zhang was a director at Shanghai Firetech Information Science and Technology Company.
In January, the DOJ had indicted two other Silk Typhoon hackers, Yin Kecheng and Zhou Shuai, revealing another Chinese tech company associated with the campaign: Shanghai Heiying Information Technology Company.
The researchers found that these companies had patent filings for tools for remote automated evidence collection, router intelligence evidence collection, computer scene rapid evidence collection, defensive equipment reverse production, intelligent home appliances evidence collection and analysis, remote cellphone evidence collection, and others that show offensive cyber capabilities.
These include capabilities that haven’t previously been publicly linked to the Silk Typhoon campaign, such as tools and methods for collecting data from Apple devices.
The researchers offer the possibility that these companies may offer cyber offensive services to multiple CCP offices, which would explain why the capabilities have not been linked to the Silk Typhoon campaign.
The new insight shows the importance of tracking threat actor groups not just by clusters of activity, the researchers said. Unmasking the hackers and their companies not only revealed their capabilities, but shed new light on whether agencies of the Chinese regime were passing on software exploits obtained elsewhere to their contractors.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Wow
0
Wow
0
 Sad
0
Sad
0
 Angry
0
Angry
0















Comments (0)